
Turning Quantum Bottlenecks into Breakthroughs
CS researchers develop a novel system that lets multiple programs run at once on a single quantum machine, promising faster scientific discoveries.

CS researchers develop a novel system that lets multiple programs run at once on a single quantum machine, promising faster scientific discoveries.

Adam Cannon is part of the first cohort of professors being honored for excellence and innovation in teaching.
Luis Gravano was honored with the 10-year Test-of-Time Award, and Eugene Wu earned multiple awards and co-hosted several events.

Every year, leading conferences across computer science honor research that has stood the test of time—work that continues to shape … Continue reading Three Professors Recognized with Test of Time Awards
At this year’s University Commencement, Columbia Engineering Dean Emeritus Zvi Galil will be presented with an honorary degree.

A driving force in the field of natural language processing, Kathleen McKeown will receive this year’s Faculty Mentoring Award bestowed at University Commencement.

Experts came together at Columbia to explore how brain science can shape the next generation of AI.
At the BRITE ’25 conference, Henry Yuen broke down and shared his insights on the pace of advancement of quantum computing and what it will likely impact in the future, and what it won’t.

A new collaboration aims to chart a path to building genuinely trustworthy AI agents.
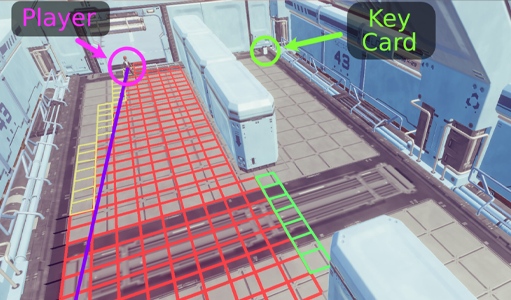
Researchers from the Computer-Enabled Abilities Laboratory (CEAL) developed a new tool to make games truly playable for blind and low-vision players.
Jason Nieh has been elected to the American Association for the Advancement of Science, one of the oldest scientific societies in the world.

The Columbia Engineering AI Demo Session held Mar. 4 in Carleton Commons showcased innovations in computer vision, robotics, sensing, and sustainability. As part of the Columbia AI Summit—a University-wide event highlighting Columbia’s deep expertise in artificial … Continue reading AI in Action

CS researchers were among the experts who considered AI from every angle at the kick-off session of the Columbia AI Summit.
The department is thrilled to introduce a cadre of new researchers poised to join the charge in artificial intelligence (AI) … Continue reading CS Welcomes Six New Faculty

Columbia University is the first academic institution to partner with Richtech Robotics Inc. in its Richtech Accelerator Program, an initiative … Continue reading Zhou Yu Joins Richtech Accelerator Program
Find open faculty positions here.
President Bollinger announced that Columbia University along with many other academic institutions (sixteen, including all Ivy League universities) filed an amicus brief in the U.S. District Court for the Eastern District of New York challenging the Executive Order regarding immigrants from seven designated countries and refugees. Among other things, the brief asserts that “safety and security concerns can be addressed in a manner that is consistent with the values America has always stood for, including the free flow of ideas and people across borders and the welcoming of immigrants to our universities.”
This recent action provides a moment for us to collectively reflect on our community within Columbia Engineering and the importance of our commitment to maintaining an open and welcoming community for all students, faculty, researchers and administrative staff. As a School of Engineering and Applied Science, we are fortunate to attract students and faculty from diverse backgrounds, from across the country, and from around the world. It is a great benefit to be able to gather engineers and scientists of so many different perspectives and talents – all with a commitment to learning, a focus on pushing the frontiers of knowledge and discovery, and with a passion for translating our work to impact humanity.
I am proud of our community, and wish to take this opportunity to reinforce our collective commitment to maintaining an open and collegial environment. We are fortunate to have the privilege to learn from one another, and to study, work, and live together in such a dynamic and vibrant place as Columbia.
Sincerely,
Mary C. Boyce
Dean of Engineering
Morris A. and Alma Schapiro Professor